What does your phone know about you? How securely does it store your data, and who can access it? Fortunately, you can now build and program your own mobile phone in just a few days. That’s exactly…
CONTINUE READING 🡒 Category: Security
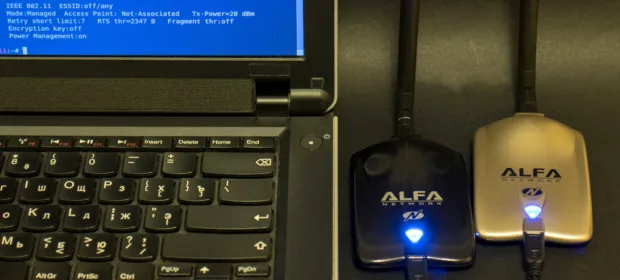
Two Alfa USB Wi‑Fi adapters are better than one: preparing…
In earlier articles on pentesting Wi‑Fi access points, we covered the basics; now it’s time for more advanced techniques. We’ll look at adapter specifics and turn up the power on our dongle. This is necessary to use…
CONTINUE READING 🡒 Inside Drone Software: How UAVs Are Programmed for Autonomous Flight
Flying a quadcopter is an art in its own right, and writing the software that lets it fly autonomously is just as exciting. In this article, I’ll show how to build a Python program to pilot a…
CONTINUE READING 🡒 Ansible: Automating System and Application Deployment
Ansible is a tool almost everyone has heard of, but it’s mostly used by system administrators. Developers and researchers typically encounter it when they need to spin up their own servers or deploy an existing configuration. That…
CONTINUE READING 🡒 How Digital Audio Encoding Works: Sampling, Quantization, Bitrate, and Codecs
Ever wondered how digital devices play back sound? How a stream of ones and zeros becomes an audible signal? If you’ve started reading, you probably have. In this article, you’ll learn how different audio formats came about,…
CONTINUE READING 🡒 Supercharge Nmap: Advanced Penetration Testing with Firewall Evasion, Dirbusting, DoS…
Nmap is the gold standard among port scanners and one of a pentester’s most important tools. But can you honestly say you’ve mastered all its features and use cases? In this article, you’ll learn how to use…
CONTINUE READING 🡒 Wardriving Hardware Guide: Building a Wi‑Fi Pentesting Toolkit with USB…
Wardriving—essentially Wi‑Fi traffic capture—always starts with choosing the right hardware. That’s exactly what we’ll do: in a handy Q&A, we’ll break down what devices are out there, which tasks they’re best suited for, and what to pick…
CONTINUE READING 🡒 Build a Custom, Debloated Windows 10 ISO the Easy Way
Building your own OS distributions is a favorite pastime among Linux enthusiasts. It’s often assumed that Windows users don’t get to enjoy anything similar. Not quite: there are ways to strip unnecessary components from a Windows 10…
CONTINUE READING 🡒 60+ Gift Ideas for Hackers: Best Geeky Gadgets for Friends…
We’ve rounded up 60+ gadgets, so you’re bound to find something to delight your geeky friends for New Year’s or any other occasion—or (we’ve all been there!) a great way to spend the gift cash from relatives…
CONTINUE READING 🡒 Unmasking Shingled Magnetic Recording in Western Digital and Seagate HDDs
Until recently, the savvy user—the kind who doesn’t mind spending a few days on forums—knew this as gospel: Seagate’s consumer drives use SMR (shingled magnetic recording), which is bad, and Western Digital’s don’t. Lots of people based…
CONTINUE READING 🡒 Crypto drainers. New scam empties crypto wallets automatically
Drainers represent a new type of phishing that is currently ravaging the cryptocurrency world. It’s growing at an incredible speed and has already surpassed ransomware in terms of prevalence and stolen funds. This article provides an insight into drainers, their operational principle, and the market that emerged on their…
CONTINUE READING 🡒 Crypto Mining Made Easy: Automate Your Operations and Optimize Performance
Lately, the mining landscape has changed fundamentally. With around a thousand altcoins now, focusing on a single cryptocurrency has become too risky. Exchange rates and mining difficulty are constantly in flux. Keeping up and manually switching to…
CONTINUE READING 🡒 Relay again. Mastering relevant NTLM Relay attack techniques implemented via…
No doubt, you’ve heard many times that the NTLM Relay support is about to be disabled in Windows. I’ve heard it many times, too, but it’s mid-2025, and I still encounter NTLM Relay in almost every project. This article discusses relevant NTLM Relay…
CONTINUE READING 🡒 Comparing 8 Home Firewalls: Which Has the Strongest Default Security?
You’d think picking a firewall for a home PC would be simple—just install it and go. But firewalls aren’t all the same, and choosing the right one can take time and effort. Today we’ll look at eight…
CONTINUE READING 🡒 DeepNude Explained: How AI Undresses Women in Photos and Drives…
DeepNude, an app that can shamelessly undress women in photos, blew up online last June. The project runs on a hellish cocktail of neural networks, artificial intelligence, and raw sexual instinct.
CONTINUE READING 🡒 Why Messaging Apps Don’t Truly Protect Your Chat Privacy—and How…
End-to-end encryption (E2EE) is often touted as a cure-all against persistent attempts by hackers and law enforcement to read online conversations. It’s commonly summarized as “the keys live only on the participants’ devices and never touch the…
CONTINUE READING 🡒 How Everyday Users Try to Hide Digital Evidence—and Why It…
Most criminals are anything but professionals, so the data-hiding methods they use are pretty crude. Yet these methods often work—simply because the investigator may not have the time or expertise to run a thorough analysis. So what…
CONTINUE READING 🡒 How to Choose and Set Up an ESP8266 Wi‑Fi Deauther
A Wi‑Fi jammer—also called a Wi‑Fi blocker—is a gadget designed to disconnect wireless devices from an access point. Such a device can be used for harmless pranks as well as for criminal purposes, for example to take…
CONTINUE READING 🡒 DIY Ultra-Cheap Zigbee and Z-Wave Hub for Smart Home Devices
Once you start building a smart home, it’s hard to stick to a single vendor. That means you’ll end up with a mishmash of standards that don’t mesh well and a lineup of hubs—each one hogging a…
CONTINUE READING 🡒 Quick Guide to Online Anonymity: Encryption Types, Traffic Protection, and…
Today, everyday users have access to a solid range of cryptographically robust encryption protocols and the software that implements them. In this article, we’ll survey the main categories of these solutions (even if many are already well…
CONTINUE READING 🡒