TP-Link has confirmed the existence of an unpatched 0-day vulnerability affecting several router models. The company said it is already investigating the issue and preparing patches.
CONTINUE READING 🡒 AI ransomware PromptLock turned out to be a research project
It has emerged that PromptLock, the AI-powered ransomware discovered last month by ESET specialists, is an academic research project by a group of researchers from New York University.
CONTINUE READING 🡒 OAuth successors. Attacks targeting OpenID Connect
OpenID Connect is a reenvisioning of the OAuth protocol; it was designed to solve the authentication problem and patch security holes in the original specification by making the standard more stringent and demanding. But people continue making mistakes, and misconfigs resulting in vulnerabilities still occur. This article…
CONTINUE READING 🡒 Python Computer Vision: Training a Neural Network for Bear vs.…
You’ve probably heard that neural networks have gotten amazingly good at recognizing objects in images lately. Our goal is to learn how to put them to work, because that power can be useful in all kinds of…
CONTINUE READING 🡒 Authorities shut down the pirate streaming network StreamEast
Egyptian authorities and the Alliance for Creativity and Entertainment (ACE) report that they have shut down StreamEast, the world’s largest illegal streaming network for live sports. Two suspected operators of the platform have been arrested.
CONTINUE READING 🡒 Apple invites researchers to test iPhone security
Apple has announced it is now accepting applications for the 2026 Security Research Device Program (SRDP). White-hat researchers interested in receiving an iPhone specifically configured for security research can apply until October 31, 2025.
CONTINUE READING 🡒 Build a Privacy-First Smartphone Without Backdoors—Why It’s Easier Than You…
What does your phone know about you? How securely does it store your data, and who can access it? Fortunately, you can now build and program your own mobile phone in just a few days. That’s exactly…
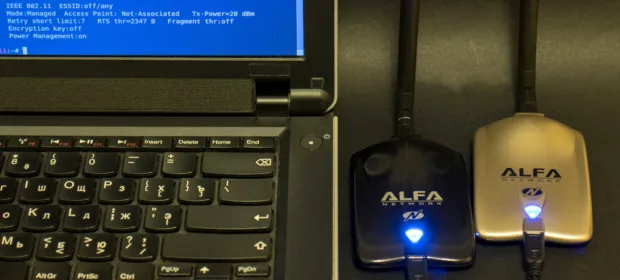
CONTINUE READING 🡒 Two Alfa USB Wi‑Fi adapters are better than one: preparing…
In earlier articles on pentesting Wi‑Fi access points, we covered the basics; now it’s time for more advanced techniques. We’ll look at adapter specifics and turn up the power on our dongle. This is necessary to use…
CONTINUE READING 🡒 Inside Drone Software: How UAVs Are Programmed for Autonomous Flight
Flying a quadcopter is an art in its own right, and writing the software that lets it fly autonomously is just as exciting. In this article, I’ll show how to build a Python program to pilot a…
CONTINUE READING 🡒 Android Code Injection with Frida: Hooking and Instrumenting Third-Party Apps
When we talk about reverse‑engineering and modifying third‑party applications, we usually mean using a decompiler, a disassembler, and a debugger. But there’s a tool that takes a very different approach: Frida—a toolkit that lets you inject into…
CONTINUE READING 🡒 Ansible: Automating System and Application Deployment
Ansible is a tool almost everyone has heard of, but it’s mostly used by system administrators. Developers and researchers typically encounter it when they need to spin up their own servers or deploy an existing configuration. That…
CONTINUE READING 🡒 Salesloft temporarily disables Drift after massive data theft
Salesloft announced that on September 5 it will temporarily disable its AI chatbot, Drift, after numerous companies were affected by a large-scale supply-chain attack targeting it. The incident resulted in the mass theft of authentication tokens.
CONTINUE READING 🡒 A hacker attack disrupted Bridgestone’s operations
The Japanese corporation Bridgestone reports that it is investigating a cyberattack that affected the operations of some of its manufacturing facilities in North America.
CONTINUE READING 🡒 Apitor Technology toys transmitted children’s geolocation data to China
The U.S. Department of Justice filed a lawsuit against toy manufacturer Apitor Technology. U.S. authorities believe the company allowed a third party from China to collect children’s geolocation data without their knowledge and without parental consent.
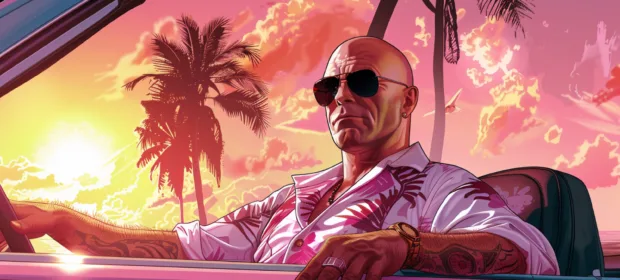
CONTINUE READING 🡒 Dangerous skin: Exploiting a glitch in GTA Vice City
Today I will demonstrate the full exploit development cycle: from creating a fuzzer to shellcode start. The target that will be exploited is a parser of BMP files embedded in GTA Vice City: the game takes these files as user skins. A correctly crafted file should cause…
CONTINUE READING 🡒 How Digital Audio Encoding Works: Sampling, Quantization, Bitrate, and Codecs
Ever wondered how digital devices play back sound? How a stream of ones and zeros becomes an audible signal? If you’ve started reading, you probably have. In this article, you’ll learn how different audio formats came about,…
CONTINUE READING 🡒 August Windows updates may block app installations
Microsoft reported that the Windows security updates for August 2025 may trigger unexpected User Account Control (UAC) prompts and cause problems with app installations. The bug affects users without administrator privileges across all supported versions of Windows.
CONTINUE READING 🡒 Hackers Are Using the HexStrike AI Tool to Exploit Newly…
Check Point analysts warned that attackers are using the new HexStrike AI framework, designed for offensive cybersecurity, to exploit recent n-day vulnerabilities in real-world attacks.
CONTINUE READING 🡒 Firewall Level 2: Configuring a MikroTik Router to Block Common…
In this article, we’ll cover how to harden a MikroTik router against attacks and port scans, and how to keep your network off blocklists. The techniques you learn here will also help you configure other types of…
CONTINUE READING 🡒 Grok is being used to spread malicious links on X
Guardio Labs analysts have observed that attackers are using Grok, the AI assistant integrated into the social network X, to circumvent link-posting restrictions that the platform has implemented to combat malicious advertising.
CONTINUE READING 🡒