Last year, I discovered a binary bug in the AdGuard driver. Its ID in the National Vulnerability Database is CVE-2022-45770. I was disassembling the ad blocker and found a way to use the identified vulnerability for local privilege escalation. As a bonus, this article gives insight into…
CONTINUE READING 🡒 Category: Security
Kung fu enumeration. Data collection in attacked systems
In penetration testing, there’s a world of difference between reconnaissance (recon) and data collection (enum). Recon involves passive actions; while enum, active ones. During recon, you use only open sources (OSINT), and the target system is not affected in any way (i.e. all…
CONTINUE READING 🡒 Serpent pyramid. Run malware from the EDR blind spots!
In this article, I’ll show how to modify a standalone Python interpreter so that you can load malicious dependencies directly into memory using the Pyramid tool (not to be confused with the web framework of the same name). Potentially, this enables you to evade…
CONTINUE READING 🡒 Attacks on the DHCP protocol: DHCP starvation, DHCP spoofing, and…
Chances are high that you had dealt with DHCP when configuring a router. But are you aware of risks arising if this protocol is misconfigured on a company’s server? Using its misconfigurations, not only can a hacker disable the DHCP server, but also deliver…
CONTINUE READING 🡒 Poisonous spuds. Privilege escalation in AD with RemotePotato0
This article discusses different variations of the NTLM Relay cross-protocol attack delivered using the RemotePotato0 exploit. In addition, you will learn how to hide the signature of an executable file from static analysis.
CONTINUE READING 🡒 Infiltration and exfiltration. Data transmission techniques used in pentesting
Imagine a situation: you managed to penetrate the network perimeter and gained access to a server. This server is part of the company’s internal network, and, in theory, you could penetrate there as well. Too bad, the compromised node is in the DMZ and doesn’t have access to the Internet.…
CONTINUE READING 🡒 Nightmare Spoofing. Evil Twin attack over dynamic routing
Attacks on dynamic routing domains can wreak havoc on the network since they disrupt the routing process. In this article, I am going to present my own modification of the Evil Twin attack designed to intercept data in OSPF-based networks. I will also demonstrate how…
CONTINUE READING 🡒 Herpaderping and Ghosting. Two new ways to hide processes from…
The primary objective of virus writers (as well as pentesters and Red Team members) is to hide their payloads from antiviruses and avoid their detection. Various techniques are used for this purpose. This paper discusses two of them: Herpaderping and Ghosting.
CONTINUE READING 🡒 SIGMAlarity jump. How to use Sigma rules in Timesketch
Information security specialists use multiple tools to detect and track system events. In 2016, a new utility called Sigma appeared in their arsenal. Its numerous functions will save you time and make your life much easier.
CONTINUE READING 🡒 Pivoting District: GRE Pivoting over network equipment
Too bad, security admins often don’t pay due attention to network equipment, which enables malefactors to hack such devices and gain control over them. What if attackers have already seized control over your peripherals? Will they be able to access the internal infrastructure?
CONTINUE READING 🡒 First Contact: Attacks on Google Pay, Samsung Pay, and Apple…
Electronic wallets, such as Google Pay, Samsung Pay, and Apple Pay, are considered the most advanced and secure payment tools. However, these systems are also plagued by vulnerabilities because they use technologies created thirty years ago. This article describes techniques…
CONTINUE READING 🡒 Ethernet Abyss. Network pentesting at the data link layer
When you attack a network at the data link layer, you can ‘leapfrog’ over all protection mechanisms set at higher levels. This article will walk you through most of the attack vectors targeting this lowest level of the network.
CONTINUE READING 🡒 Gateway Bleeding. Pentesting FHRP systems and hijacking network traffic
There are many ways to increase fault tolerance and reliability of corporate networks. Among other things, First Hop Redundancy Protocols (FHRP) are used for this purpose. In this article, I will explain how pentesters interact with FHRP in the course of network attacks.
CONTINUE READING 🡒 Top 5 Ways to Use a VPN for Enhanced Online…
This is an external third-party advertising publication.
CONTINUE READING 🡒 Challenge the Keemaker! How to bypass antiviruses and inject shellcode…
Recently, I was involved with a challenging pentesting project. Using the KeeThief utility from GhostPack, I tried to extract the master password for the open-source KeePass database from the process memory. Too bad, EDR was monitoring the system and prevented me from doing this: after…
CONTINUE READING 🡒 Vulnerable Java. Hacking Java bytecode encryption
Java code is not as simple as it seems. At first glance, hacking a Java app looks like an easy task due to a large number of available decompilers. But if the code is protected by bytecode encryption, the problem becomes much more complicated. In this article,…
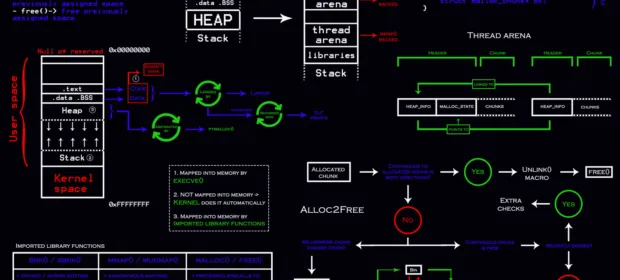
CONTINUE READING 🡒 Climb the heap! Exploiting heap allocation problems
Some vulnerabilities originate from errors in the management of memory allocated on a heap. Exploitation of such weak spots is more complicated compared to ‘regular’ stack overflow; so, many hackers security researchers have no idea how to approach them. Even the Cracking the Perimeter (OSCE) course doesn’t…
CONTINUE READING 🡒 Quarrel on the heap. Heap exploitation on a vulnerable SOAP…
This paper discusses a challenging CTF-like task. Your goal is to get remote code execution on a SOAP server. All exploitation primitives are involved with the heap in one way or another; so, you’ll learn a lot about functions interacting with it. Also, you’ll…
CONTINUE READING 🡒 Routing nightmare. How to pentest OSPF and EIGRP dynamic routing…
The magic and charm of dynamic routing protocols can be deceptive: admins trust them implicitly and often forget to properly configure security systems embedded in these protocols. In this article, I will explain what nightmares can occur if the network admin doesn’t take a good care…
CONTINUE READING 🡒 First contact. Attacks on chip-based cards
Virtually all modern bank cards are equipped with a special chip that stores data required to make payments. This article discusses fraud techniques used to compromise such cards and methods used by banks to protect cardholders against attackers.
CONTINUE READING 🡒