Analysts at Binarly have discovered at least 35 images on Docker Hub that are still infected with the backdoor that infiltrated xz Utils last year. The researchers warned that this potentially puts users, organizations, and their data at risk.
Binarly explains that many CI/CD pipelines, developers, and production systems pull images directly from Docker Hub, using them as the base for their own containers. If those images are compromised, every new build will inherit the vulnerability or malicious code.
Recall that the backdoor in the popular XZ Utils package was accidentally discovered in 2024, and the incident received significant attention. As a result, the issue was assigned the identifier CVE-2024-3094, and it received a score of 10 out of 10 on the CVSS scale.
Because xz Utils and its bundled liblzma library are very popular and included in most Linux distributions (and are also used by many applications for Linux and macOS), the discovery of the malware has shaken the entire open-source community.
An investigation conducted last year showed that the backdoor operation was carefully planned and spanned several years, with the attackers spending a long time preparing their attack and gaining the trust of the xz Utils maintainer, Lasse Collin (aka Larhzu).
The backdoor intercepted and redirected SSH RSA key decryption operations (the RSA_public_decrypt function) in OpenSSH through the IFUNC mechanism of the glibc library. As a result, if an attacker connected via SSH to the compromised system using a special private key, they could bypass authentication and remotely execute commands with root privileges.
Since the malicious code ultimately shipped in the official packages of Linux distributions (for example, Debian, Fedora, openSUSE, and Red Hat), the XZ Utils infection became one of the most serious compromises of last year.
As Binarly specialists reported this week, the supply-chain issues caused by the XZ Utils compromise are still relevant, as dozens of infected images remain on Docker Hub.
“We discovered that some of these compromised images [due to XZ Utils] are still publicly available on Docker Hub. And what’s worse—additional images were built on top of these infected base images, leading to a cascading infection,” the researchers say.
In total, specialists found 35 such images that are still available for download. The analysts emphasize that this number only partially reflects the true scale of the problem, as they did not perform a full scan of the platform.
Researchers were most surprised by the fact that the Debian developers did not remove the 64-bit images with the infected version of the library from Docker Hub.
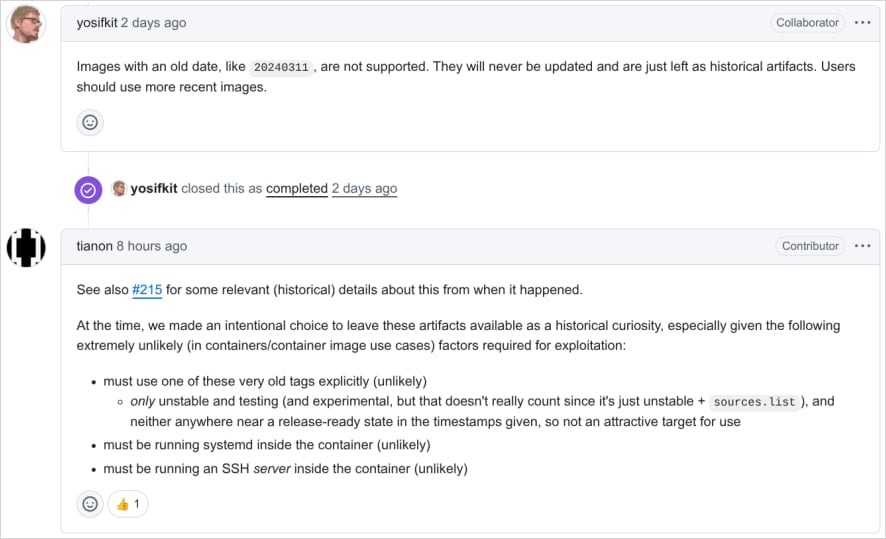
In response, Debian stated that they deliberately chose not to remove these images from the repository and preserved them as historical artifacts. At the same time, users are strongly advised to work only with current images rather than old ones.
The maintainers say they made this decision because they considered exploitation unlikely. For example, to use the backdoor, sshd must be installed and running in the container, the attacker must have network access to the container’s SSH service, and they must use a private key that matches the backdoor’s activation logic.
Binarly experts criticized this approach, emphasizing that the mere public availability of these images creates a significant risk of accidental downloading or use in automated builds.
The same applies to all images that may contain a compromised version of XZ Utils. The researchers remind users to always manually verify that the library is present in a safe version 5.6.2 or newer (the latest stable version is 5.8.1).
“The XZ Utils backdoor incident demonstrates that even malicious code introduced for a short time can go unnoticed in official container images for an extended period and can spread throughout the Docker ecosystem,” the experts conclude. “This underscores that such artifacts can persist and propagate stealthily in CI/CD pipelines and container ecosystems, and it confirms the critical need for continuous monitoring at the binary level, rather than merely tracking versions.”

2025.04.29 — FBI Offers 10 million USD for information on Salt Typhoon members
The FBI offers up to 10 million USD for information about members of the Chinese hacker group Salt Typhoon and last year's attack that had…
Full article →
2025.01.23 — Fake Telegram CAPTCHA forces users to run malicious PowerShell scripts
Hackers used the news of Ross Ulbricht pardoning to lure users to a rogue Telegram channel where they are tricked into running malicious PowerShell code. This…
Full article →
2025.01.25 — 18,000 script kiddies have been infected with backdoor via XWorm RAT builder
According to CloudSEK analysts, malefactors attack novice hackers using a fake malware builder. Script kiddies' systems become infected with a backdoor that steals data and subsequently…
Full article →
2025.02.08 — Hackers exploit RCE vulnerability in Microsoft Outlook
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) warned Federal Civilian Executive Branch (FCEB) Agencies that they have to secure their systems from ongoing…
Full article →
2025.01.22 — Fake Homebrew Infects macOS and Linux Machines with infostealer
Attackers use Google ads to disguise themselves as the Homebrew website and distribute malware targeting Mac and Linux systems and stealing logon credentials, browser data, and cryptocurrency wallets.…
Full article →
2025.03.18 — Black Basta ransomware group developed its own automated brute-forcing framework
According to EclecticIQ, Black Basta Ransomware-as-a-Service (RaaS) group has developed its own automated brute-forcing framework dubbed BRUTED. It's used to hack edge network devices…
Full article →
2025.01.29 — Google to disable Sync in older Chrome versions
Google announced that in early 2025, Chrome Sync will be disabled in Chrome versions older than four years. Chrome Sync enables users to save and sync their…
Full article →
2025.04.25 — Asus patches vulnerability in AMI's MegaRAC enabling attackers to brick servers
Asus released patches for the CVE-2024-54085 vulnerability that allows attackers to seize and disable servers. The security hole affects the American Megatrends International (AMI) MegaRAC Baseboard Management…
Full article →
2025.03.10 — Nearly a million Windows computers impacted by a malvertising campaign
According to Microsoft, nearly 1 million Windows devices fell victim to a sophisticated malvertising campaign in recent months. Cybercriminals were able to steal credentials, cryptocurrency, and sensitive…
Full article →
2025.04.22 — Scammers pose as FBI IC3 specialists, offer 'assistance' to fraud victims
According to the FBI, scammers impersonating employees of the FBI Internet Fraud Complaint Center (IC3) contact fraud victims offering them 'assistance' in getting their money…
Full article →