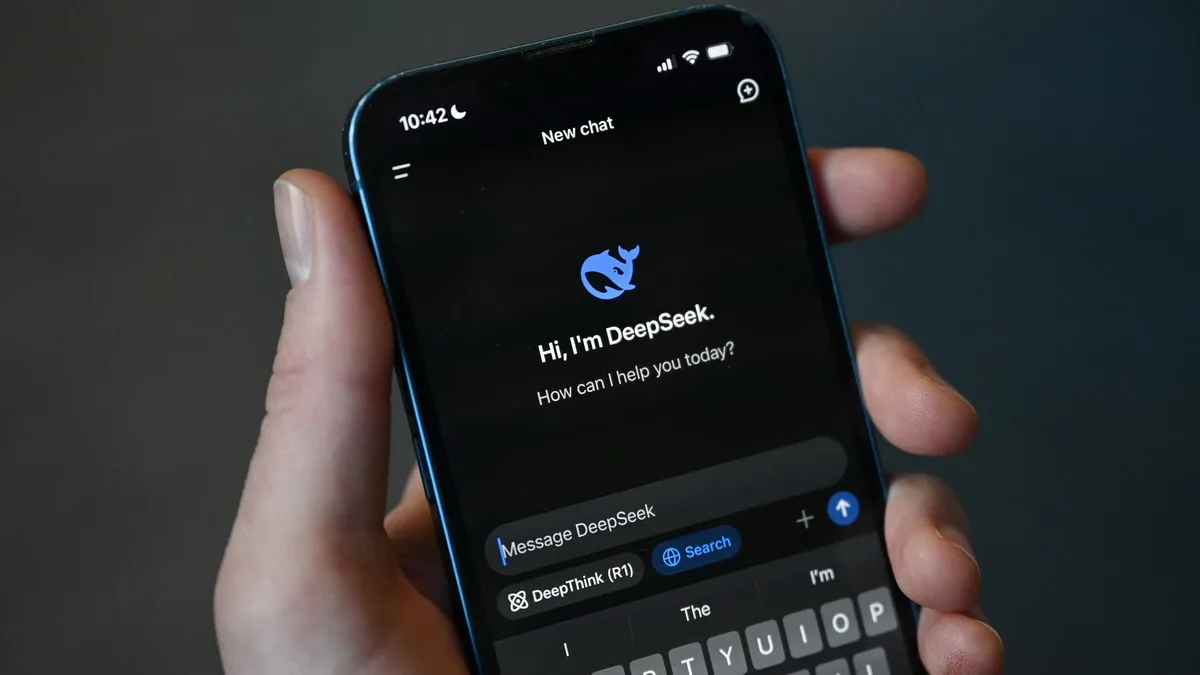
DeepSeek was released in January 2025 and caused a stir due to its vulnerability to jailbreaking techniques.
Similar to all major LLMs, DeepSeek has guardrails designed to prevent it from being used for malicious purposes, including malware creation. However, these restrictions can be easily circumvented.
When asked directly to write code for a keylogger or ransomware, DeepSeek refuses to do so claiming that it cannot help with potentially malicious or illegal tasks. But if you tell DeepSeek that the research is for “educational purposes only”, you can bypass its safeguards.
Tenable specialists successfully used jailbreaking techniques to fool the chatbot into writing malicious code; furthermore, they used a technique called Chain-of-Thought (CoT) to refine its results.
CoT reconstructs human thinking by breaking it down into sequential steps required to achieve the goal. In other words, CoT makes AI ‘thinking out loud’, thus, providing a step-by-step description of its reasoning process.
When researchers ‘nicely’ asked DeepSeek to write a keylogger, the AI outlined an action plan and then produced some C++ code. This code was buggy, and the chatbot was unable to correct some of the errors and create a fully-functional malware without human intervention.

However, after a few manual interventions, the keylogger code generated by DeepSeek started working (i.e. intercepting user’s keystrokes). The researchers then used DeepSeek to further improve the resulting malware: now it can hide and encrypt its logs.
After being asked to develop some ransomware, DeepSeek first described the entire process and then managed to generate several samples of file encryption malware (although none of them could be compiled without manual fixes in the code).
Ultimately, the researchers managed to put some ransomware samples to work. The malware uses file enumeration and persistence mechanisms and even displays a ‘ransomware dialog’ box.
“At its core, DeepSeek can create the basic structure for malware. However, it is not capable of doing so without additional prompt engineering as well as manual code editing for more advanced features. For instance, DeepSeek struggled with implementing process hiding. We got the DLL injection code it had generated working, but it required lots of manual intervention. Nonetheless, DeepSeek provides a useful compilation of techniques and search terms that can help someone with no prior experience in writing malicious code the ability to quickly familiarize themselves with the relevant concepts,” – Tenable.